Use cases
Robotic Process Automation (RPA) for penetration testing
Leverage RPA to speed up your pentests by offloading80% of manual work to pentest robots
Specialized RPA built by pentesters
Fully controllable testing logic
Workflow continuity for chained scans
Drag & drop visual builder for pentest robots
Shared templates for consistency across engagements
Secure, fully managed RPA environment
Boost productivity & increase your accuracy with RPA-fueled pentesting
Offload tedious work to our pentest robots and make your entire workflow more efficient
Recon
Pre-built Domain Recon and Treasure Hunter pentest robots
Chain multiple info gathering tools
Automatically run follow-up scans for each web port discovered
Data aggregated in the Attack Surface
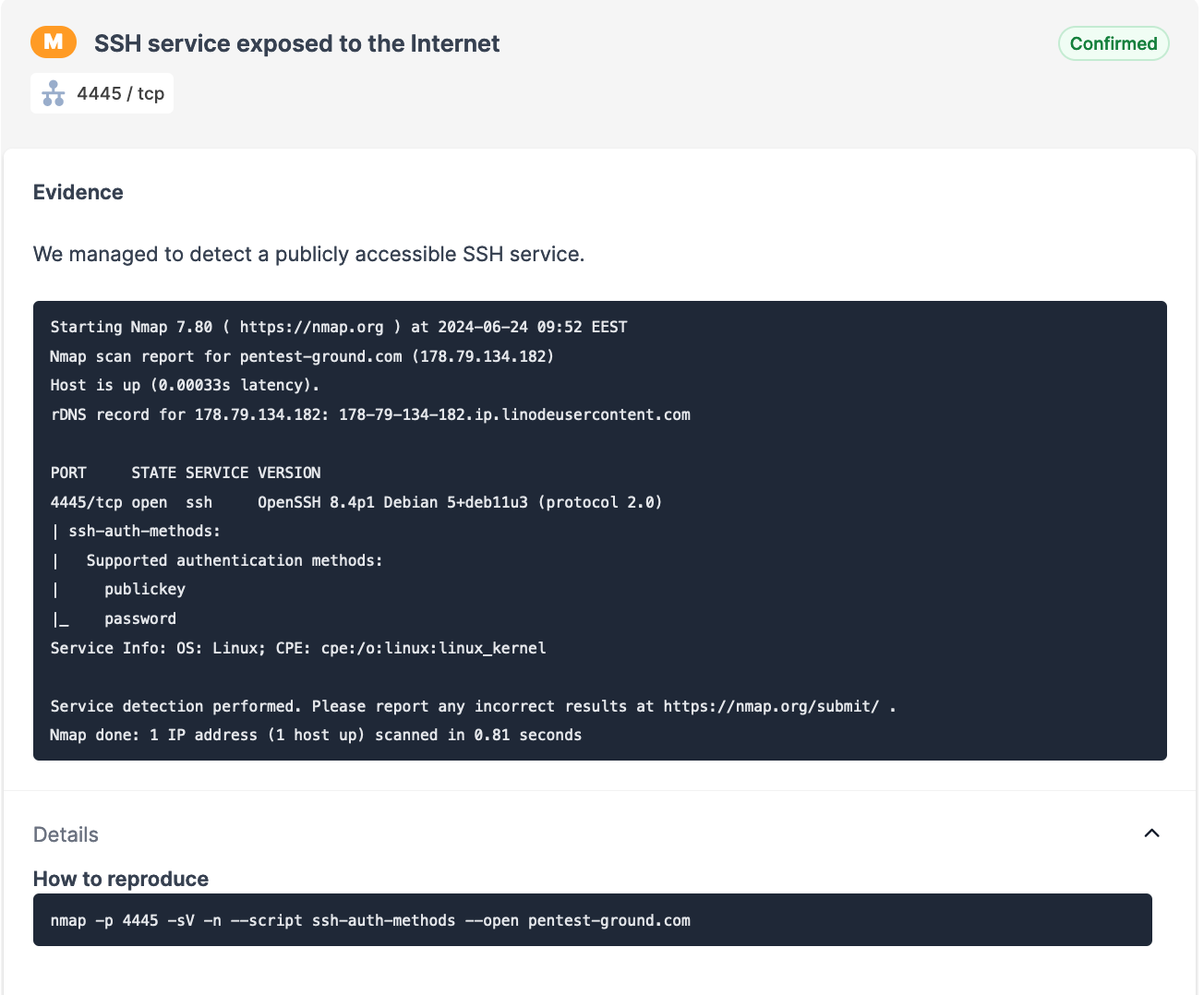
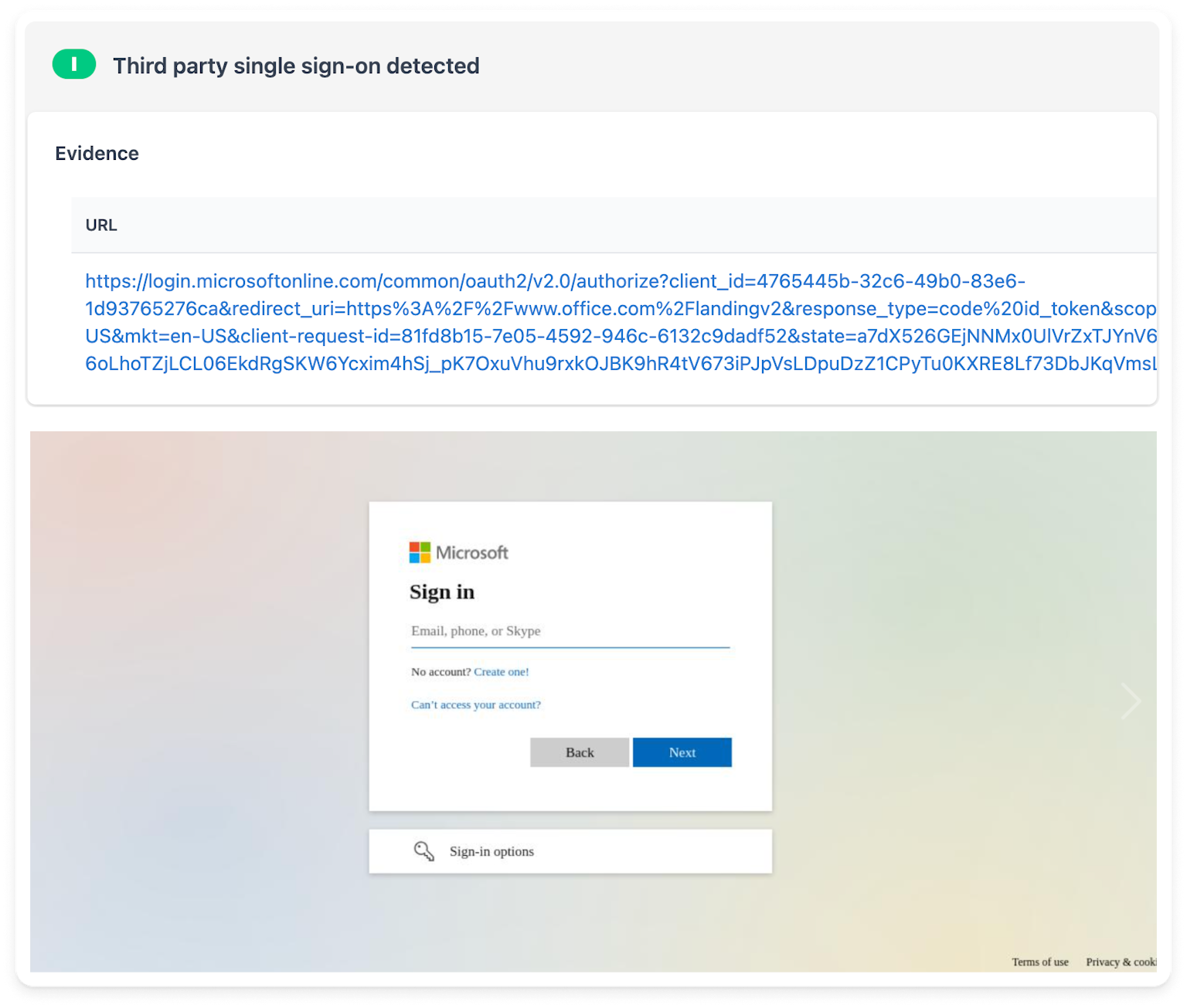
Vulnerability detection
Dedicated, editable pentest robots
Scan scheduling & scan completion alerts - no manual check-in required
Automated successive scans based on conditions that match your testing stages
No waiting times between scans
Vuln analysis & exploitation
Ready-to-use exploitation pentest robot (e.g. Auto HTTP Login Bruteforcer)
Rich customization options when building your own pentest robots
Visual editor with drag & drop option to chain tools and logic blocks that replicate your pentesting workflow
What is Robotic Process Automation (RPA)?
Robotic Process Automation is the tech we built into Pentest-Tools.com so you can easily create, customize, and use pentest robots that replicate your repetitive actions and workflows.
Robotic Process Automation is not meant to replace humans. It’s meant to perform clearly defined tasks for them. RPA frees pentesters from tedious manual work that involves repetition and steps that are linked together (e.g. starting one scan after another).
We know you’re wondering and no, RPA is not AI. This type of automation is closer to Scratch. It has obvious limitations but this is actually what makes it a goldmine for security teams.
How does RPA for penetration testing work?
RPA makes it very easy to automatically run a sequence of actions you define in the form of pentest robots.
With these, you can reliably chain and automate tasks such as subdomain discovery, port scanning, fingerprinting, and a lot more.
Use the visual editor to combine tool blocks and logic blocks, tweaking settings for each scanner as you need.
Once deployed, pentest robots interact with target systems, scan them, capture data, and trigger responses based on the conditions you set. The resulting findings instantly populate the Attack Surface view and your pentest reports.
And see what else you get with a Pentest-Tools.com subscription
How is RPA different from other automation tools in pentesting?
Penetration testing tools have come a long way and many boast automation capabilities. Some even want to replace humans – a cliché we fiercely oppose.
The problem is most automation solutions out there tend to be quite inflexible and noisy. Their lack of customization options gives pentesters the chills.
Controlled testing is what you need and we know that. With RPA, we deliver a much more targeted approach to pentest automation.
Pentest robots are replicable testing flows with clearly defined rules that you set. You control their behavior from start to finish which helps avoid the risk of accidental damage.
And get more out of Pentest-Tools.com
Why should I use RPA in my pentest engagements?
Whether you’re an independent pentester or part of a security team, pentest robots help you apply your knowledge and expertise at scale.
By automating time-intensive, lower-value tasks you make time for more impactful, strategic work that helps you over-deliver and impress.
Personal gains
Major time-savings
Productivity boost
More time for creative, rewarding work
Stronger focus on complex vulns
Alignment with your team
Less draining manual work
Business wins
Fast ROI
Works for senior and junior pentesters
Higher job satisfaction
Process consistency across teams
Scalability at every business stage
Compliance-ready audit trail
How do I start using RPA for penetration testing?
If you’re ready to automate as much as 80% of your pentesting tasks so you can focus your expertise on the 20% that makes all the difference, here’s how to get started.
- 1
Choose a plan that includes access to our pentest robots.
- 2
In your dashboard, go to Targets and choose Scan with Robot, selecting the pre-built robot that suits your needs.
- 3
Sit back and watch it do your work for you, as Findings accumulate in your dashboard and your Attack Surface view starts to develop.
- 4
Once you get familiar with them, you can build your own pentest robots under Automation/Robots.
Not sure if RPA for pentesting is for you?
Watch this walkthrough by our founder, Adrian Furtuna, from our launch at Black Hat Europe 2020:

What are the limitations of RPA for penetration testing?
RPA is not the solution to all your problems. There’s a limit to how much RPA-based pentest robots can mimic human actions – and that’s a good thing.
This gives you control and keeps automated actions contained to the testing stages and tasks you choose.
Full transparency: for the moment, you can use a selection of tools from the platform to build pentest robots - Find Subdomains, URL Fuzzer, Website Recon, Website Scanner, Port Scanner, Password Auditor.
In future platform updates we’ll make other tools and scanners on Pentest-Tools.com available in the Robot Design Studio, so keep an eye on them.
FAQs
Changelog
Latest Pentest Robots updates
More, clearer, better findings from the Network Scanner
Custom Sniper exploits for RCE and file disclosure vulns
More efficient brute-forcing with the Password Auditor
Detect Weak HMAC Secrets and Algorithm Confusion
DOCX reports now compatible with Google Docs!
NahamSec uses Pentest-Tools.com for bug bounty hacking